-

Supply Chain Ransomware: How Third-Party Attacks Impact Major Companies
In recent years, ransomware attacks have become a familiar threat, but in recent months a particularly dangerous pattern has become clearer: attacks aimed at one…
-

SOC Evolution: From Alert Handling to Risk Control
For years, Security Operations Centers were built around one core mission: detect alerts, investigate them, and respond as quickly as possible. Speed mattered more than…
-

Two Phishing Attacks That Show How Even Tech Giants Remain Vulnerable
August 2025 delivered a sharp reminder that even organizations with advanced security infrastructures are not immune to phishing and social engineering. Two separate attacks, one…
-

HMRC Phishing Incident Leads to £47M Tax Fraud
A few days after a large scale phishing related incident affected the United Kingdom online tax services, it is already clear that this was not…
-

Why Most Security Tools Miss What Employees Do on Their Phones
For many organizations, security strategy is still built around laptops, corporate networks, and cloud systems. That is where most controls are deployed, most budgets are…
-

Millions of Passwords Leaked – and the Real Risk Is Only Beginning
In June 2025, it was revealed that approximately 6.5 million LinkedIn user passwords were shared on dark web forums. This was not a breach of…
-
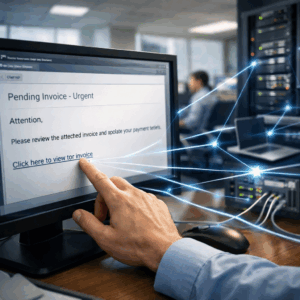
Attention! User Awareness Alone Cannot Stop Phishing
Organizations invest significant resources in employee training, phishing simulations, and security awareness programs. This is important, but it is no longer sufficient. Modern phishing does…
-
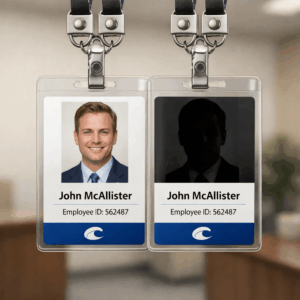
BEC is Not an Email Attack. It is an Identity Attack
In most organizations, Business Email Compromise is still viewed as just another type of phishing attack aimed at sending a convincing email. In practice, this…
-

Telecom and Cybersecurity: A Strategic Partnership
In a world where phishing attacks, fraud, and impersonation increasingly originate from mobile devices and communication networks, telecom companies have become the first line of…
