-
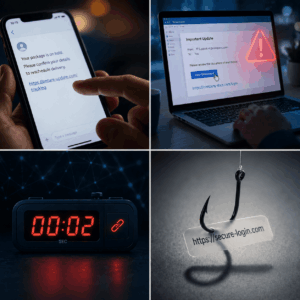
The Security Gap That Happens in Seconds
Many organizations today rely on a large number of security tools.There are systems that monitor networks, systems that detect threats, systems that analyze user behavior,…
-
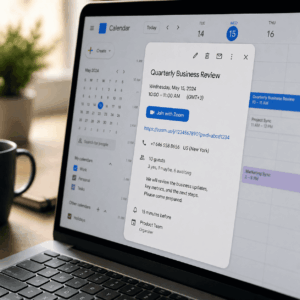
Another Evolution of Phishing: Attacks That Start With a Zoom Meeting
Phishing attacks continue to evolve, and a recent campaign attributed to the North Korean hacking group BlueNoroff shows just how sophisticated these methods are becoming.…
-

Sometimes Hackers Don’t Need to Hack
For years, organizations invested heavily in firewalls, network defenses, and sophisticated security infrastructure. But many modern attacks no longer start by breaking into systems. Instead,…
-
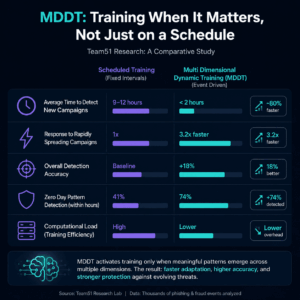
Team51 Research: Scheduled Training vs. Dynamic Training in Phishing Detection
In most machine learning systems, training happens in fixed cycles.Models are updated once a day, once a week, or after a certain volume of data…
-

When Security Becomes a Bottleneck
Security is meant to protect the organization, but in many cases, it also starts to impact how fast the organization can move. This does not…
-

Security Tools vs. Security Outcomes
Most organizations feel secure because they have “a lot” in place – multiple systems, layered defenses, and a constant stream of alerts. On paper, it…
-

The Hidden Gap Between Detection and Action
There is a moment when a threat is detected.An alert appears, logs start to accumulate, and it feels like things are under control. But in…
-
AI-Driven Social Engineering: The Threat Landscape for 2026
AI is turning social engineering attacks into operations that are more sophisticated, faster, larger in scale, and highly personalized. Instead of targeting simple human mistakes,…
-
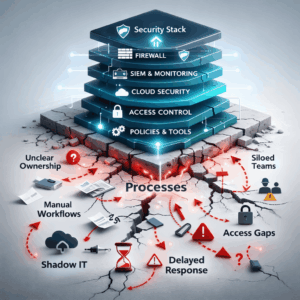
The Security Stack is Strong. The Processes are Weak.
In most organizations, the security stack looks impressive. There are advanced systems, dedicated budgets, leading vendors, and well-organized reports. On paper, everything seems under control.…
