-
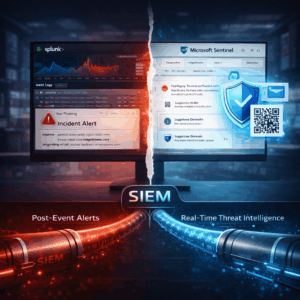
Why SIEM Without Real-Time Phishing Intelligence Is Only Half the Picture
Organizations today invest heavily in SIEM platforms like Splunk and Microsoft Sentinel, and for good reason. These systems are essential for centralizing security events, analyzing…
-

Cyber Fraud Overtakes Ransomware. Enterprise Security in 2026
For years, ransomware attacks were considered the primary cyber threat to organizations. They were loud, disruptive, and made headlines. But in recent years, a quieter…
-
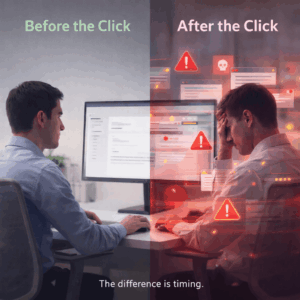
After the Click, You’re Already Late
In a meeting with a large organization, backed by a strong SOC and a broad security stack, the message was clear from the start:“We’re covered.…
-
Team51 Research: Phishing Attacks Are Shifting from Email to the Browser
For many years, email was the primary attack vector for phishing. Most security systems, organizational awareness efforts, and employee training programs were built around this…
-

Phishing-as-a-Service: One of the Top Trends of 2025
One of the most important developments this year is the sharp rise of Phishing as a Service (PhaaS) platforms.Pre built phishing infrastructures that are sold…
-

A Routine Approval That Turned Into a Financial Loss
It started with a completely ordinary action.A short message. A request for approval. Something that looked like part of the daily workflow. An employee in…
-
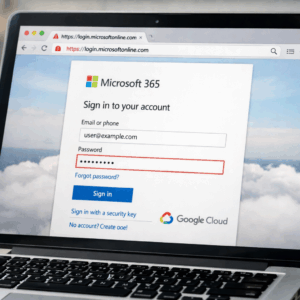
Phishing Campaign Abusing Google Cloud Targets Microsoft 365 Accounts
A recent phishing campaign demonstrates how legitimate cloud services can be abused to compromise enterprise Microsoft 365 accounts, without using malware, exploits, or compromised infrastructure.…
-

Understanding the Latest Phishing Trends: Insights from Q4 2025 Reports
Introduction:Phishing remains the top threat to organizations in 2025, but the landscape is evolving rapidly. Recent reports from KnowBe4 (October 2025) and SpyCloud (December 2025)…
-

The Cost of One Click: How Small Security Gaps Become Business Risks
In many organizations, security incidents are still associated with large-scale breaches, sophisticated attacks, or system-wide failures. But in reality, some of the most damaging incidents…
