One of the most interesting things about real-world security incidents is that they almost never look the way people imagine. No alarms, no systems going down, no internal headlines.
In one customer case, it started with a completely standard phishing message. The user reported it, the email was flagged, and from the organization’s perspective, the incident was closed. Nothing unusual on the surface.
A few days later, unusual logins began to appear across internal services. Not break-in attempts, not brute force activity, but legitimate use of existing permissions. Some of the access came from a mobile device, some through services that were not directly connected to the email system.
The challenge was not detecting the initial attack, but realizing that something was still happening after the alert disappeared from the dashboard. Quietly, without clear indicators, and without a single “incident” anyone could easily point to.
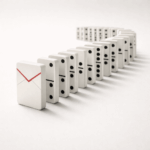
This is not an exceptional case. In most organizations, the gap forms right here: between point-in-time detection and continuous understanding of what users actually do, across channels, over time.
Most of the damage does not come from the click itself, but from the time that passes afterward.